- A Digital Video Recorder is an embedded system that converts analog camera signals into compressed digital video for structured long-term storage.
- DVR architecture centralizes video encoding after analog ingestion, using hardware-accelerated codecs and embedded Linux for predictable multi-channel performance.
- DVR reliability depends on bitrate planning, disk subsystem design, encoder capacity limits, time synchronization, and hardened network security controls.
When discussing Digital Video Recorders with security professionals, most understand their function but not their architecture. A DVR is a purpose-built embedded system that converts analog video into digital streams, compresses them using hardware codecs, and stores them while enabling live view, playback, and network access. It is optimized for deterministic performance and sustained multi-channel recording under continuous write conditions.
Unlike a Network Video Recorder, which processes video already encoded at the camera, or a Video Management System, which provides orchestration software, a DVR performs centralized encoding after analog ingestion. In environments with existing coaxial infrastructure, this architecture preserves cabling investments while enabling high-definition recording and modern compression.
Historical and Technical Evolution of DVR Systems
From Tape to Embedded Appliances
The DVR emerged from the limitations of analog VCR based CCTV systems, where video retention depended on magnetic tape rotation schedules and manual intervention. Early digital systems relied on PC based platforms with PCI capture cards that digitized analog signals and compressed them using software codecs. These systems were powerful for their time but suffered from operating system instability, high power consumption, and inconsistent long term reliability.
The transition to embedded Linux appliances marked a turning point. Manufacturers began integrating multi channel decoders, hardware encoding engines, and storage controllers into single SoCs. This reduced mechanical failure points and improved predictability under continuous load. By removing general purpose desktop operating systems from the equation, embedded DVRs delivered higher uptime and tighter resource control, which remains foundational to modern platforms.
Evolution of HD over Coax and Hybrid Systems
As resolution demands increased, traditional composite video became insufficient. HD over coax standards such as TVI, CVI, and AHD allowed megapixel resolution transmission across existing RG59 and RG6 cabling. DVR platforms adapted by integrating higher bandwidth decoders and more powerful encoding blocks capable of handling 1080p and 4K inputs.
Hybrid DVR systems further expanded architectural flexibility by supporting a limited number of IP camera inputs alongside analog channels. This hybridization created a transitional path for organizations that wanted to gradually migrate to IP without abandoning analog infrastructure. From an engineering standpoint, hybrid systems require careful bandwidth and encoder allocation to balance analog and IP streams within the same processing envelope.
End to End System Architecture
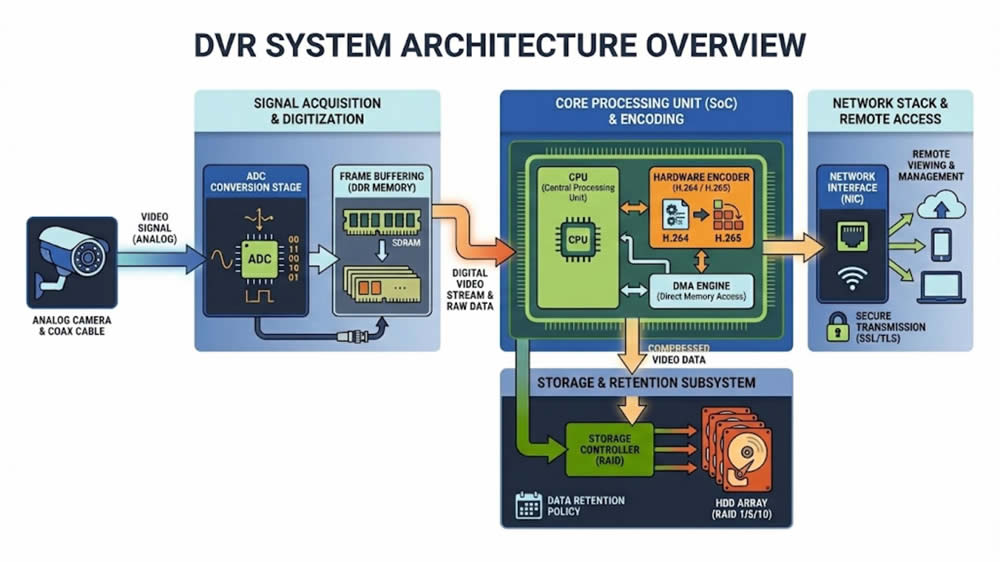
Signal Acquisition Pipeline
The signal acquisition stage begins with an analog camera output transmitted over coaxial cable. Depending on deployment, the signal may conform to NTSC, PAL, or an HD over coax variant. At the DVR input, front end conditioning circuits stabilize voltage and filter noise before the waveform reaches multi channel decoder ICs. These decoders convert analog signals into digital frame data using high precision ADC components.
Frame synchronization is critical in multi channel systems. Each channel must be time aligned for accurate playback and cross camera analysis. Internally, frames are buffered in DDR memory before being dispatched to hardware encoders. Any instability in the analog front end can cascade into compression inefficiencies, higher bitrates, and degraded image clarity.
Embedded Processing Architecture
Modern DVR platforms are built around SoCs that integrate CPU cores, video processing units, memory controllers, and peripheral interfaces. The operating environment is typically embedded Linux, which provides process isolation and hardware abstraction while remaining lightweight. Video encoding is offloaded to dedicated hardware blocks, ensuring that compression tasks do not compete with user interface or networking processes.
Resource orchestration inside the SoC is precise. The CPU manages tasks such as:
- Web interface rendering
- Configuration management
- Log generation
- Network protocol handling
Meanwhile, hardware encoders handle macroblock processing and rate control. DMA engines transfer frame data efficiently between memory and encoder units, minimizing CPU overhead and ensuring deterministic performance under sustained load.
Video Encoding Engine
Compression is the core of storage efficiency. Most DVRs implement hardware-accelerated versions of H.264 and H.265. The encoding engine organizes frames into GOP structures that include I frames for full image references and P or B frames for predictive compression.
Several rate control strategies are commonly used:
- Constant Bitrate for predictable network allocation
- Variable Bitrate for optimized storage efficiency
- Capped VBR for balancing peak usage and quality
Encoding decisions directly influence retention modeling. Longer GOP intervals reduce storage usage but may increase recovery time during playback scrubbing. Engineers must tune frame rate, resolution, and GOP length collectively rather than in isolation.
Storage Architecture and Retention Engineering
Disk Subsystem Design
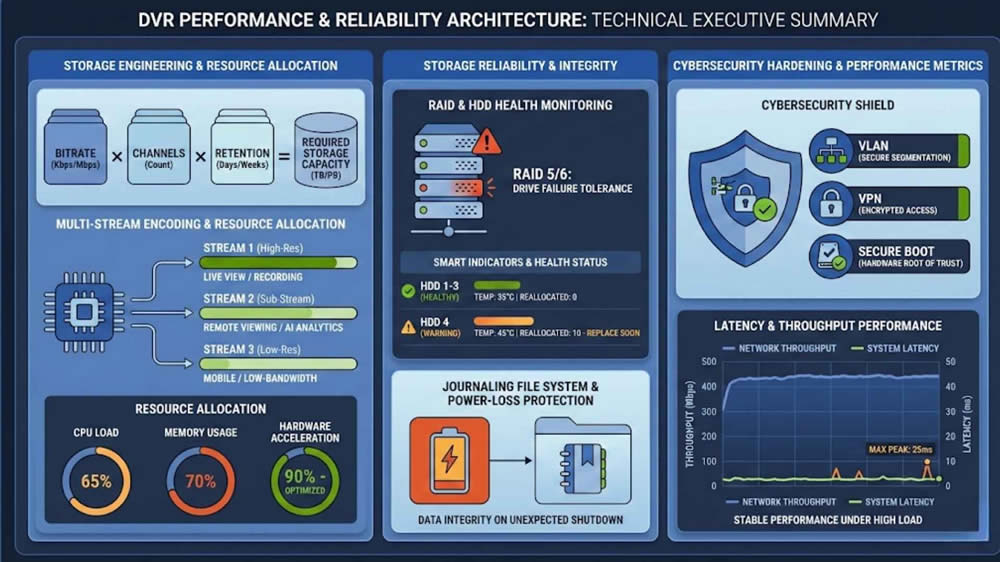
The storage subsystem in a DVR is optimized for continuous sequential writes. Surveillance-grade hard drives are engineered to sustain high duty cycles and tolerate elevated temperatures associated with continuous operation. SATA controllers distribute data across one or more drives, depending on system capacity.
Some deployments incorporate RAID configurations for redundancy. RAID 1 or RAID 5 may provide protection against single disk failure, though rebuild operations can temporarily reduce throughput. Engineers must evaluate whether redundancy justifies the performance overhead in a given risk profile.
Retention Modeling and Throughput Planning
Retention planning begins with a straightforward formula but requires contextual refinement. At a basic level, engineers evaluate:
- Bitrate per channel
- Number of channels
- Recording hours per day
- Required retention duration
Real world variables alter this calculation. Motion intensity, scene complexity, and recording mode all influence average bitrate. Event driven recording can dramatically extend retention in low activity environments. Engineers must also ensure that peak write rates during high motion periods do not exceed disk throughput limits.
File Structure and Data Integrity
DVRs typically use proprietary container formats designed for efficient indexing and playback. These containers store metadata such as timestamps, channel identifiers, and event flags alongside compressed video data. Index tables allow rapid time based search without scanning entire disk segments.
To preserve integrity, many systems implement journaling mechanisms that protect against corruption during power loss. SMART monitoring and periodic disk health checks provide early warning of impending failure. Data integrity must be engineered proactively rather than assumed.
Performance Engineering and Throughput Analysis
Channel Density and Encoder Limits
Channel capacity is constrained by decoder bandwidth and encoder macroblock throughput. A system rated for 16 channels at 1080p may not sustain full frame rate on all channels simultaneously. Engineers must understand aggregate macroblock processing limits to avoid oversubscription.
Throughput modeling includes:
- Total incoming resolution across channels
- Frame rate per channel
- Simultaneous playback sessions
- Network streaming load
Ignoring cumulative load often results in unexpected performance degradation during peak usage.
Latency Considerations
Latency arises at multiple stages, including encoding buffer delays, disk I O scheduling, and network transmission. Live view latency depends on buffer depth and display pipeline optimization. Playback latency increases when disk seeks become fragmented under concurrent read and write activity.
Reducing latency may require shorter GOP intervals and lower buffer thresholds. However, these adjustments can increase storage consumption. Engineering decisions must weigh operational responsiveness against retention efficiency.
Resource Allocation and Multi Stream Management
Many DVRs generate both a main stream and a sub stream for each channel. The main stream is recorded at full resolution, while the sub stream supports remote viewing at reduced bitrate. This dual encoding consumes additional hardware resources.
Concurrent operations that affect performance include:
- Multiple remote viewing sessions
- Simultaneous multi channel playback
- Backup or export processes
Careful capacity planning ensures that no single operation compromises recording stability.
Networking and Remote Access Architecture
Embedded Network Stack
Although DVRs originate from analog ecosystems, they are deeply networked devices. Embedded network stacks support HTTP or HTTPS interfaces, RTSP streaming, and sometimes ONVIF interoperability. Web based management portals operate through lightweight internal servers.
Remote connectivity often relies on NAT traversal or relay services. Engineers must understand how these mechanisms establish outbound connections and what exposure they create. Transparent network architecture reduces uncertainty and security risk.
Bandwidth Optimization
Dual stream configurations allow remote users to access lower bitrate feeds while preserving high quality recordings locally. Adaptive bitrate strategies reduce congestion when network conditions fluctuate. Frame rate throttling can further conserve bandwidth without degrading evidentiary quality.
In enterprise deployments, collaboration with IT teams is essential. Surveillance traffic should be modeled within overall network capacity planning. Proper bandwidth allocation prevents interference with other mission-critical services.
Integration into Structured IT Environments
Integrating DVR systems into managed networks requires disciplined configuration. Common best practices include:
- VLAN segmentation
- Strict firewall rules
- Static IP assignments
- VPN based remote access
Treating DVRs as managed infrastructure components rather than standalone appliances improves visibility and security posture. Centralized logging and authentication can further enhance operational oversight.
Cybersecurity Architecture and Hardening
Threat Surface Analysis
From a cybersecurity perspective, DVR systems must be treated as networked compute devices rather than passive recording appliances. Firms that emphasize rigorous security standards often communicate this expertise through authoritative corporate brand storytelling initiatives that reinforce engineering credibility. Historically, many DVR deployments suffered from weak default credentials, exposed services, and inconsistent firmware patching practices. Because DVRs often sit at the edge of a network with external access enabled for remote viewing, they can become attractive targets for credential attacks, botnet enrollment, or service exploitation.
The primary attack surface typically includes:
- Web management interfaces
- RTSP streaming ports
- Proprietary mobile application services
- Peer to peer relay connections
Even if the DVR itself is not directly exposed to the public internet, lateral movement inside a compromised LAN can reach it. For this reason, segmentation and internal access controls are just as important as perimeter defense. In professional deployments, I evaluate the DVR’s exposure profile in the same way I would evaluate any server class system.
Secure Design Principles
A professionally engineered DVR deployment starts with validating firmware integrity. Secure boot mechanisms verify digital signatures before executing the operating system, which prevents unauthorized firmware modifications. Digitally signed update packages reduce the risk of supply chain or interception based tampering during maintenance cycles.
Administrative access control must also be granular. Role based access control allows separation of duties between operators, supervisors, and system administrators. Password policies should enforce complexity and periodic rotation. Where supported, HTTPS with valid certificates should replace plain HTTP to prevent credential interception. Hardening is not a single configuration step but a structured discipline that spans firmware, authentication, and transport security.
Network Level Hardening
At the network layer, reducing exposed services is one of the most effective mitigation strategies. Disabling unused ports, deactivating automatic port mapping services, and avoiding universal plug and play configurations limit unintended exposure. VPN based remote access models are preferable to direct port forwarding because they centralize authentication and encryption.
Additional protective measures often include:
- VLAN isolation for surveillance devices
- Access control lists restricting lateral communication
- Intrusion detection monitoring for anomalous traffic
Security posture improves significantly when DVR systems are included in formal vulnerability management processes rather than treated as isolated hardware assets.
DVR vs NVR: Deep Technical Comparison
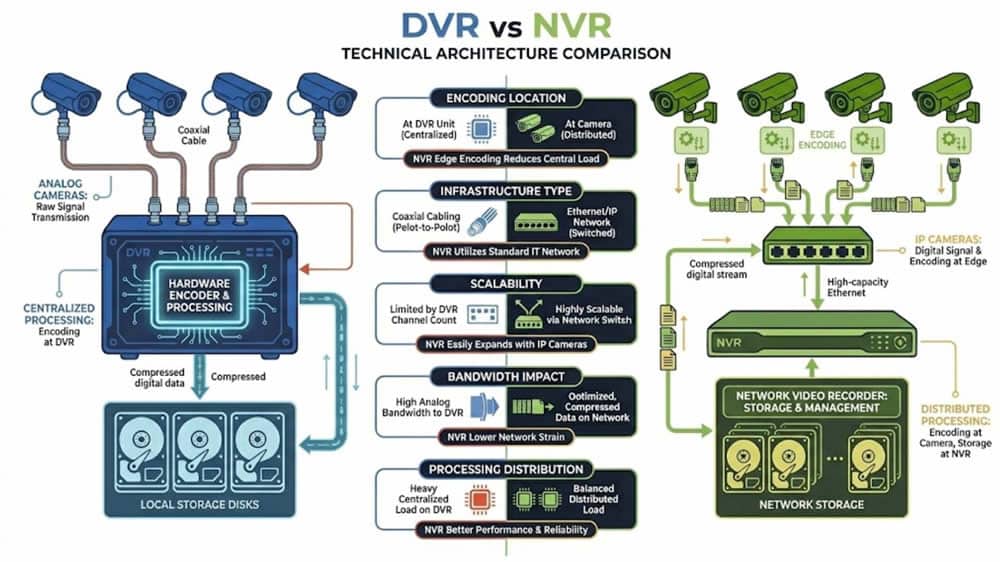
Processing Distribution
The architectural distinction between DVR and NVR platforms lies in where compression occurs. In a DVR architecture, analog signals are digitized and encoded centrally. In contrast, IP cameras in an NVR architecture encode video at the edge before transmitting compressed streams to the recorder. This redistribution of computational responsibility alters system behavior under load.
Centralized encoding simplifies camera hardware and can reduce per camera cost. However, it concentrates processing load within the recorder chassis. Distributed encoding reduces recorder CPU requirements but increases camera complexity and power consumption. When evaluating system design, I always assess not just aggregate throughput but also fault domains. In a centralized model, encoder failure impacts multiple channels. In a distributed model, individual camera failures are isolated.
Infrastructure Requirements
DVR systems leverage coaxial cable infrastructure, often already present in retrofit facilities. Power can be delivered centrally or through power over coax depending on system design. NVR systems rely on Ethernet cabling and commonly use Power over Ethernet switches to supply cameras.
Infrastructure evaluation includes:
- Cable type and maximum run distances
- Power budget and redundancy
- Network switch capacity
- Physical routing constraints
In established facilities with extensive coax installations, DVR solutions can dramatically reduce upgrade complexity. In new construction environments where Ethernet is standardized, NVR architectures may align more naturally with IT governance models.
Scalability Constraints
Scalability in DVR systems is bounded by physical input ports and encoder capacity. Expanding beyond the recorder’s native channel limit requires additional units. In NVR systems, expansion involves adding cameras and scaling storage and network bandwidth accordingly.
However, scalability is not infinite in either architecture. DVR channel limits are explicit and predictable. NVR scalability depends heavily on switch backplane capacity, uplink bandwidth, and storage array performance. In both cases, professional engineering requires explicit throughput modeling rather than relying on theoretical maximums.
Advanced Installation and System Design
Channel Planning and Capacity Forecasting
Channel planning should consider both present needs and realistic growth projections. Selecting a recorder with modest overhead capacity can prevent premature hardware replacement. At the same time, over-specifying channel count without sufficient encoder throughput can lead to performance compromise.
Effective planning includes:
- Mapping physical camera locations to recorder inputs
- Balancing high motion and low motion scenes
- Accounting for simultaneous playback demand
In multi recorder deployments, distributing channel load evenly across units improves redundancy and thermal balance.
Cable Engineering and Signal Integrity
Signal quality is heavily influenced by coaxial cable characteristics. RG59 remains common for moderate distances, while RG6 offers lower attenuation for extended runs. Proper termination and shielding practices reduce susceptibility to electromagnetic interference.
Ground loop issues can degrade image clarity and introduce noise. Isolation transformers or proper grounding techniques mitigate these risks. From my experience, many intermittent image quality complaints originate not from encoding limitations but from poor physical layer practices.
Power Architecture and Reliability
Power stability is foundational to DVR reliability. Centralized power supplies simplify maintenance but can create single points of failure. Distributed adapters isolate faults but increase management complexity. Power over coax solutions integrate power delivery with signal transmission, reducing cabling but requiring careful load calculation.
Uninterruptible Power Supply integration allows graceful shutdown and prevents file system corruption during outages. Runtime planning should account for recorder draw, camera consumption, and network switch load. Reliable power design directly correlates with reduced data integrity incidents.
Video Analytics and Intelligent Processing
Motion Detection Algorithms
Traditional motion detection relies on pixel differential analysis between consecutive frames. Advanced implementations incorporate vector analysis and region of interest segmentation to reduce false positives. Sensitivity thresholds must be tuned relative to environmental factors such as lighting shifts or foliage movement.
Selecting the appropriate model requires evaluating available processing headroom, uniformity of analytic requirements, and impact on encoding throughput. Organizations frequently support operator training with structured security training video programs that clarify how analytic configurations affect performance and retention.
Metadata Indexing and Search Optimization
Metadata management defines how efficiently recorded content can be retrieved. DVR systems embed timestamps, channel identifiers, and event markers into structured index tables. Efficient indexing allows operators to search by time window, channel, or event type without scanning raw file segments.
Search performance depends on:
- Index granularity
- Disk read optimization
- Caching mechanisms
When indexing structures are well designed, playback remains responsive even with large retention archives.
Recorder Based vs Edge Analytics
In hybrid systems, analytics may run at the camera level or within the recorder. Recorder based analytics centralize management and configuration. Edge analytics distribute computational load but may vary in capability across camera models.
Selecting the appropriate model requires evaluating:
- Available processing headroom
- Uniformity of analytic requirements
- Impact on encoding throughput
The primary rule remains that analytics must not compromise recording stability or evidentiary clarity.
Forensic Reliability and Evidence Management
Time Synchronization and Integrity
Accurate timestamps underpin evidentiary value. DVR systems should synchronize with reliable Network Time Protocol sources and maintain consistent time zone configuration. Even minor clock drift can undermine credibility in investigative contexts.
Embedding timestamps directly into video frames provides visible validation. Regular verification of synchronization status is advisable, particularly in segmented environments.
Export Validation and Hashing
When exporting video, integrity verification is essential. Many systems generate cryptographic hash values such as MD5 or SHA variants to confirm that exported files remain unaltered. Digital watermarking techniques may further detect manipulation attempts.
Evidence handling protocols should include:
- Documented export procedures
- Controlled access to exported media
- Preservation of original metadata
Technical rigor in export validation strengthens defensibility during legal proceedings. When organizations highlight these capabilities publicly, they often incorporate them into a broader results-driven video marketing strategy to demonstrate operational integrity.
Playback Stability Under Stress
Multi channel playback during investigations can impose heavy read loads on storage subsystems. Efficient indexing and caching mitigate performance degradation. Engineers should test playback scenarios involving simultaneous scrubbing across several channels.
Disk fragmentation and long term wear can affect playback responsiveness. Periodic health audits and proactive drive replacement reduce the likelihood of critical playback failure during high pressure review situations.
Firmware Architecture and Lifecycle Management
Firmware Structure and Modularity
DVR firmware typically consists of several layers, including bootloader, kernel, application services, and web interface modules. The bootloader initializes hardware components and validates firmware integrity before launching the operating system. The kernel provides scheduling and device abstraction.
Application services manage recording logic, storage indexing, networking, and user interface operations. Modular firmware design enables targeted updates without disrupting core recording functionality. Understanding this layered architecture aids in precise troubleshooting and risk assessment.
Update Governance and Rollback Strategy
Firmware updates should follow structured governance rather than ad hoc application. Testing in controlled environments prior to mass deployment prevents widespread configuration disruption. Compatibility with existing camera firmware and analytics modules should be verified.
A sound update strategy includes:
- Version tracking documentation
- Clear rollback procedures
- Maintenance windows with monitoring
Minimizing downtime during updates is critical in environments requiring continuous recording.
Reliability Engineering and Thermal Management
Thermal performance significantly influences component longevity. Sustained encoding and disk writing generate heat that must be dissipated effectively. Fan speed curves, airflow design, and rack placement all contribute to stable operation.
Mean Time Between Failure metrics provide statistical insight but must be interpreted within environmental context. Proactive disk replacement based on operational hours rather than reactive failure reduces risk exposure. Reliability engineering is an ongoing discipline rather than a one time specification exercise.
System Interoperability and Integration
External System Integration Pathways
DVR platforms frequently extend beyond standalone recording by integrating with complementary security systems. Alarm input and output terminals allow motion detectors, glass break sensors, or door contacts to trigger event-based recording. Access control integration enables credential swipes to be time-synchronized with corresponding video footage, strengthening investigative accuracy.
Common integration pathways include:
- Point of sale transaction overlays for loss prevention
- API access for third-party analytics or facility software
- Central monitoring station connectivity for remote event escalation
When engineered properly, interoperability transforms a DVR from a passive recording device into an operational intelligence node. In enterprise environments, these integrations are often validated through technical walkthrough videos that document trigger logic, synchronization accuracy, and system response behavior.
Operational Impact of Interoperability
Interoperability directly enhances situational awareness. Correlating credential activity with video events reduces investigative time and improves evidentiary reliability. Transaction overlays allow immediate alignment between financial records and camera footage, limiting ambiguity during audits or internal reviews.
The engineering value lies in structured integration design. Event triggers must be reliably mapped, timestamps must remain synchronized across systems, and APIs must be secured against unauthorized access. When these integration layers are properly configured, DVR systems contribute meaningfully to operational efficiency rather than functioning as isolated recording appliances.
Troubleshooting and Diagnostic Methodology
Fault Domain Isolation
Effective troubleshooting begins with disciplined isolation of the failure domain. Video loss may originate from camera hardware, cabling faults, power supply instability, or decoder input failure. Compression artifacts may be attributable to insufficient bitrate allocation, encoder overload, or signal degradation at the analog front end.
Initial diagnostic steps typically include:
- Reviewing system and event logs
- Verifying camera power and signal continuity
- Confirming encoder channel configuration
- Inspecting network connectivity in hybrid environments
By segmenting the signal path into discrete stages, professionals can narrow the scope of investigation quickly and avoid speculative adjustments that introduce new variables.
Performance and Storage Diagnostics
Beyond signal integrity, performance issues often emerge from storage or processing constraints. Disk failure, insufficient write speed, or degraded RAID arrays can manifest as recording gaps. CPU saturation or encoder overload may lead to dropped frames or degraded compression quality.
A structured performance review generally includes:
- Checking disk health and SMART status
- Monitoring CPU and encoder utilization
- Testing network throughput and latency
- Verifying retention and overwrite policies
Understanding internal architecture accelerates resolution. Professionals who grasp signal flow, encoding thresholds, and storage behavior diagnose root causes far more effectively than those responding solely to visible symptoms.
Engineering Decision Framework
Infrastructure Assessment Criteria
Selecting a DVR solution requires disciplined evaluation rather than preference-based assumptions. I assess channel count requirements, existing coax infrastructure, retention duration, encoder capacity, cybersecurity posture, and lifecycle maintenance obligations before recommending architecture.
Key evaluation factors include:
- Total camera density and expansion projections
- Required frame rates and resolution standards
- Storage retention mandates
- Network segmentation and access control policies
Facilities with substantial coaxial investment and stable channel counts often benefit from DVR architectures that provide predictable performance and contain infrastructure complexity.
Alignment with Operational Requirements
In contrast, environments requiring distributed scalability, centralized IT governance, or advanced analytics may require alternative architectures. The correct solution depends on operational priorities, not trend alignment. A system designed around its intended use case will outperform one selected solely for perceived modernization.
When engineered thoughtfully, a Digital Video Recorder remains a technically reliable and efficient component within surveillance infrastructure. The strength of the system lies not in its label, but in how precisely its design aligns with operational and technical constraints.
Final Thoughts
A Digital Video Recorder is a purpose-built embedded system designed for sustained, multi-channel recording with predictable performance. Its effectiveness depends on disciplined bitrate planning, encoder capacity management, storage design, and secure network configuration. When engineered properly, it delivers stable retention and reliable playback under continuous load.
Understanding DVR architecture is essential to long-term reliability. Throughput modeling, time synchronization, firmware governance, and cybersecurity hardening determine whether a system withstands operational stress and forensic scrutiny. Treated as managed infrastructure rather than a basic appliance, a DVR remains a technically sound and defensible recording platform.
LocalEyes: Your Strategic Video Production Partner
At LocalEyes, we understand that technology such as Digital Video Recorders plays a critical role in capturing and preserving visual information. But recording footage is only one part of the equation. Transforming video into a powerful communication tool that drives engagement, builds trust, and communicates expertise requires strategic production and professional storytelling.
That is where we come in. As one of America’s premier video production companies, we have produced more than 3,900 videos for over 300 clients nationwide, earning more than 500 five star reviews across platforms such as Clutch, DesignRush, and Google. With over seven years of consistent growth and recognition on the Inc. 5000 list for three consecutive years, we have built our reputation on delivering measurable results with Emmy Award winning production quality.
From our California headquarters and full service offices in Atlanta, Austin, Boston, Chicago, Dallas, Denver, Los Angeles, Miami, New York City, and San Diego, we provide testimonial, product, brand, corporate, explainer, educational, promotional, event, and animation video production services across the United States.
Whether you are showcasing advanced security infrastructure, explaining complex technical systems, or elevating your brand presence, our team combines local market expertise with enterprise level capabilities to produce video content that performs. If you are ready to turn your technical expertise into compelling visual storytelling, connect with us at LocalEyes and let’s create something that moves your audience to action.

Founder at LocalEyes Video Production | Inc. 5000 CEO | Emmy Award Winning Producer